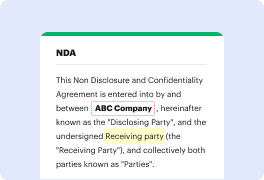
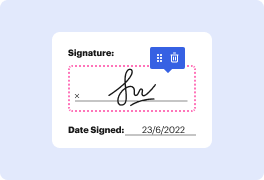
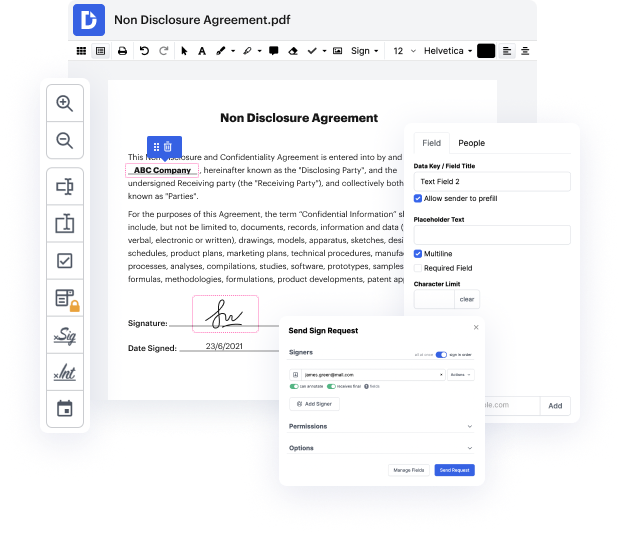
Are you having a hard time finding a reliable solution to Affix Tentative Field Release For Free? DocHub is made to make this or any other process built around documents much easier. It's straightforward to explore, use, and make edits to the document whenever you need it. You can access the core features for handling document-based workflows, like signing, importing text, etc., even with a free plan. Moreover, DocHub integrates with different Google Workspace apps as well as services, making document exporting and importing a breeze.
DocHub makes it easier to edit documents from wherever you’re. In addition, you no longer need to have to print and scan documents back and forth in order to certify them or send them for signature. All the essential features are at your fingertips! Save time and hassle by completing documents in just a few clicks. Don’t hesitate another minute and give DocHub {a try today!
A classic use-after-free vulnerability is demonstrated in heap level 2 of exploit-exercises.com. The code features a big while loop inside main, printing the auth variable which points to an auth struct with name and integer attributes, as well as a service variable that points to a string in memory. Input is then read from standard input with a secure fgets read. Various commands are checked for, including auth, reset, service, and login. Initially, both auth and service pointers are when the program starts.
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



