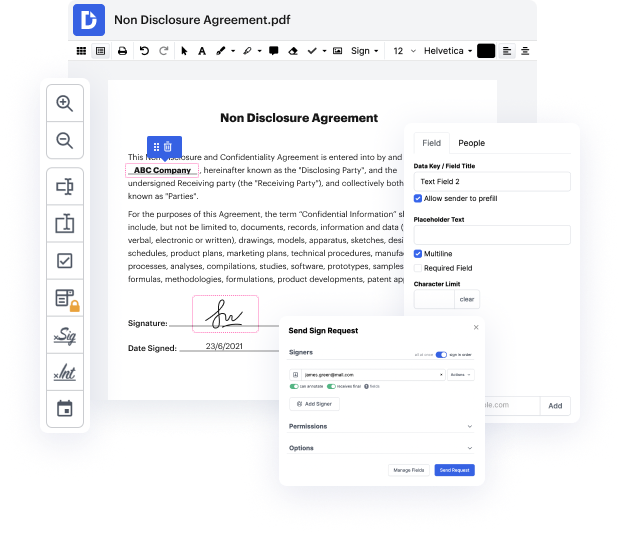
Are you looking for an editor that will let you make that last-minute tweak and Affix Approve Application For Free? Then you're in the right place! With DocHub, you can quickly apply any needed changes to your document, no matter its file format. Your output paperwork will look more professional and structured-no need to download any heavy-wight software. You can use our editor at the convenience of your browser.
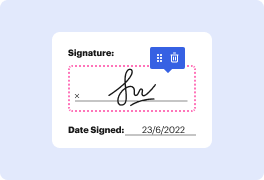
When using our editor, stay reassured that your data is encrypted and shielded from prying eyes. We comply with major data protection and eCommerce regulations to ensure your experience is safe and enjoyable every time! If you need assistance with editing your document, our dedicated support team is always here to answer all your questions. You can also take advantage of our comprehensive knowledge hub for self-assistance.
Try our editor now and Affix Approve Application For Free effortlessly!
A common use-after-free vulnerability is demonstrated in heap level 2 of exploit-exercises.com. The code includes a while loop in main that prints the auth pointer, pointing to an object with a name and integer attributes, and a service pointer, both of which are addresses. Input is read with a secure fgets function, preventing buffer overflow. The program checks for commands like auth, reset, service, and login. Initially, both auth and service pointers are .
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



