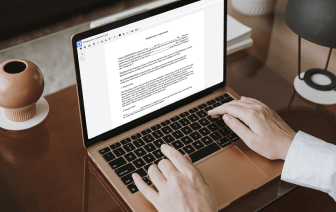
Document generation and approval are a central priority of every organization. Whether handling sizeable bulks of documents or a particular agreement, you must remain at the top of your productiveness. Getting a perfect online platform that tackles your most frequentl record creation and approval difficulties may result in quite a lot of work. A lot of online apps offer you only a restricted list of editing and signature functions, some of which may be helpful to handle cgi formatting. A platform that handles any formatting and task might be a outstanding choice when selecting program.
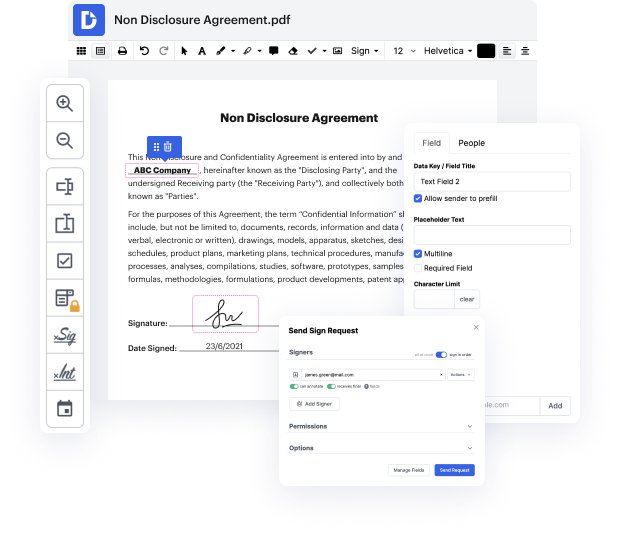
Take document management and creation to another level of simplicity and excellence without picking an difficult program interface or costly subscription plan. DocHub offers you tools and features to deal successfully with all document types, including cgi, and carry out tasks of any difficulty. Change, manage, and produce reusable fillable forms without effort. Get complete freedom and flexibility to adjust flag in cgi anytime and securely store all your complete files within your user profile or one of many possible incorporated cloud storage apps.
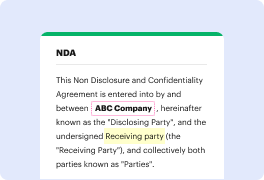
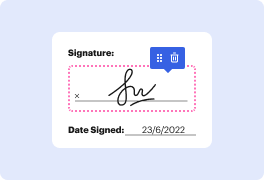
DocHub provides loss-free editing, eSignaturel collection, and cgi management on a professional level. You do not have to go through tedious tutorials and invest a lot of time figuring out the application. Make top-tier secure document editing an ordinary process for your day-to-day workflows.
with so many red team security certifications focusing on hands-on practical skills anymore i figured it was a good idea to create a series in it pro tv that would address that i call it hands-on hacking and you know what i wanted to give you a little taste of what that actually looks like coming up next all right so the first thing i did was i downloaded a vulnerable virtual machine from vulnhub.com dont worry the link for that will be in the description below and this one is called mercury its a very straightforward ctf and so i thought it was perfect for us to get our feet wet on what it looks like for us to do this hands-on hacking series build our methodology use those hacking skills that were learning to some avail right so first thing i did was i ran an nmap scan to check out for ports now ive pre-gamed a bit of this to save some time but you will be able to see the actual commands that i use so lets start off with this file right here and map all ports this was my all sca