Safety should be the primary factor when searching for a document editor on the web. There’s no need to spend time browsing for a trustworthy yet cost-effective tool with enough functionality to Adapt design in Security Employment Application. DocHub is just the one you need!
Our solution takes user privacy and data safety into account. It meets industry regulations, like GDPR, CCPA, and PCI DSS, and constantly improves its compliance to become even more hazard-free for your sensitive information. DocHub allows you to set up two-factor authentication for your account settings (via email, Authenticator App, or Backup codes).
For that reason, you can manage any paperwork, such as the Security Employment Application, risk-free and without hassles.
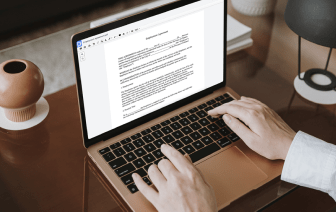
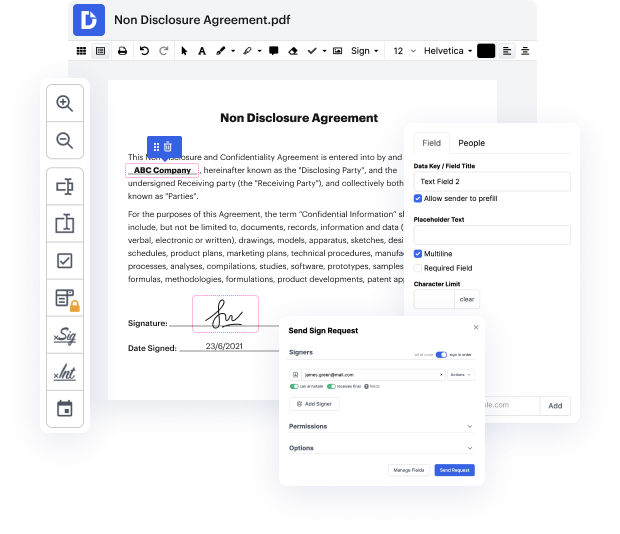
In addition to being trustworthy, our editor is also extremely straightforward to work with. Follow the instruction below and ensure that managing Security Employment Application with our service will take only a few clicks.
If you often manage your paperwork in Google Docs or need to sign attachments received in Gmail rapidly, DocHub is also a good option to choose, as it perfectly integrates with Google services. Make a one-click file upload to our editor and accomplish tasks within minutes instead of continuously downloading and re-uploading your document for editing. Try DocHub today!
in this lesson we explore the two sets of security architecture design principles described in domain 3 of the cissp common body of knowledge the purpose of designing a security architecture is to ensure security requirements are properly implemented in systems further the architecture helps prevent or respond to attempts to compromise confidentiality integrity or availability organizations must build security into design implementation and management of new and existing systems this enables safe operation that reasonably and appropriately manages risk associated with affected system and data classification and categorization security architecture design can apply to both systems and the network infrastructure security architecture design is based on one or more risk assessments its important that the security architect understand the risk associated with the data and critical systems involved during the architecture design the architect might encounter design elements that mitigate r