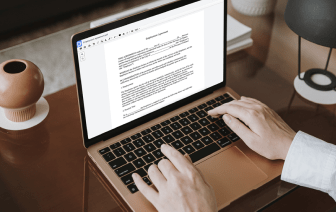
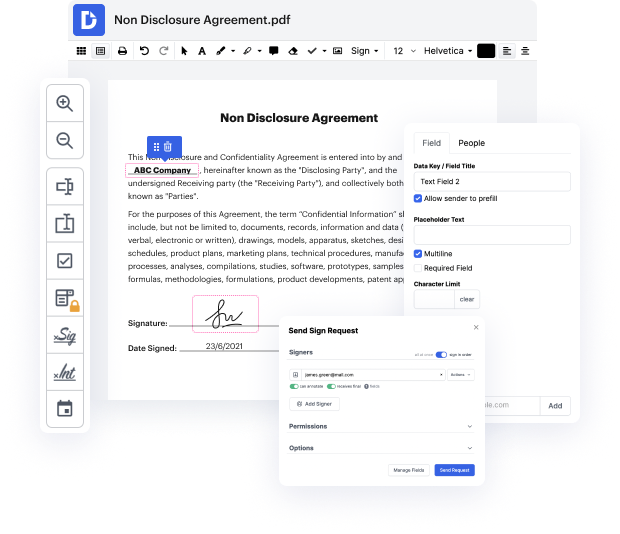
Editing ACL is fast and simple using DocHub. Skip downloading software to your PC and make alterations using our drag and drop document editor in just a few quick steps. DocHub is more than just a PDF editor. Users praise it for its efficiency and robust capabilities that you can use on desktop and mobile devices. You can annotate documents, create fillable forms, use eSignatures, and deliver documents for completion to other people. All of this, combined with a competitive cost, makes DocHub the perfect decision to adapt authentication in ACL files with ease.
Make your next tasks even easier by turning your documents into reusable templates. Don't worry about the protection of your records, as we securely store them in the DocHub cloud.
our next section weamp;#39;re going to look at the dynamic access lists or lock and key access lists on the iOS that is used to open a temporarily a temporary hole in an access list based on authentication into the router now some of the potential applications of this for traffic moving from the inside Network to the outside network is that a user would first have to authenticate before they send traffic out to the public network so for example if we want to allow them to use only Port 80 for web browsing but they first have to authenticate with the username and password before theyamp;#39;re actually allowed inbound then on the flip side as weamp;#39;re going from outside to inside we could say that maybe thereamp;#39;s an internal web server that we want people in the public network to docHub but they first have to authenticate as theyamp;#39;re coming in from the outside now in general this feature has been replaced by a more scalable and manageable ver version of it tha