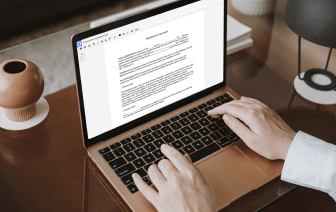
Document generation and approval certainly are a key priority for each firm. Whether dealing with sizeable bulks of files or a distinct agreement, you should stay at the top of your productiveness. Getting a excellent online platform that tackles your most frequentl record generation and approval difficulties might result in quite a lot of work. Many online apps provide merely a limited set of editing and eSignature functions, some of which could be beneficial to manage LOG formatting. A platform that handles any formatting and task will be a outstanding choice when picking software.
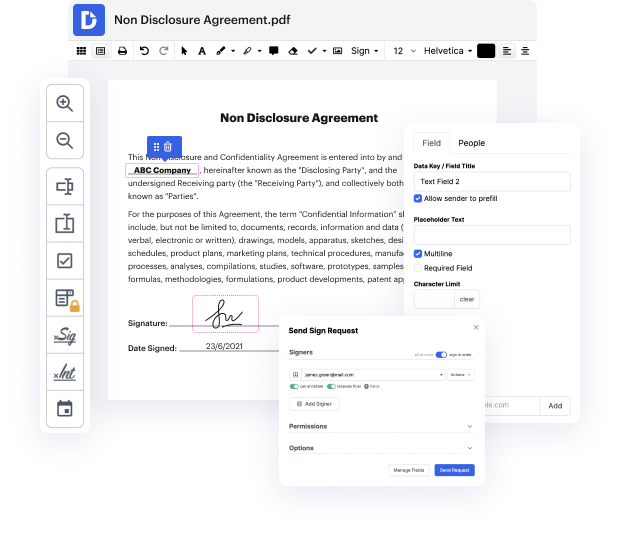
Get document management and generation to a different level of straightforwardness and excellence without choosing an awkward program interface or high-priced subscription plan. DocHub provides you with tools and features to deal efficiently with all document types, including LOG, and perform tasks of any complexity. Edit, organize, and create reusable fillable forms without effort. Get full freedom and flexibility to undo pattern in LOG at any time and securely store all your complete documents in your profile or one of many possible incorporated cloud storage space apps.
DocHub provides loss-free editing, signature collection, and LOG management on a professional level. You do not have to go through tedious tutorials and spend countless hours figuring out the platform. Make top-tier secure document editing an ordinary practice for your daily workflows.
now that we understand the different ways of logging lets talk about different recovery protocols the first one undo logging is one of the basic recovery protocols as we will see undo logging does not use right ahead logging that we covered earlier and it uses the force and steel mechanisms in terms of buffer pool management there are four types of lock records in an undo log start commits or abort of a transaction and finally an update record which states that transaction t wants to update data elements x and x previous value was v the idea behind undo logging is as follows we want to use the lock such that when we need to recover we will undo the effects of all the transactions that have not been committed on the other hand for all the transactions that have been committed we want to leave them alone in order to implement this behavior we need to establish a few rules regarding how we do logging and when to flush the dirty lock and data pages specifically there are two rules that w