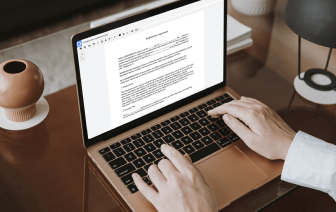
When you deal with diverse document types like Product Evaluation, you are aware how important precision and attention to detail are. This document type has its specific format, so it is essential to save it with the formatting intact. For this reason, working with such documents might be a challenge for traditional text editing software: a single wrong action may mess up the format and take additional time to bring it back to normal.
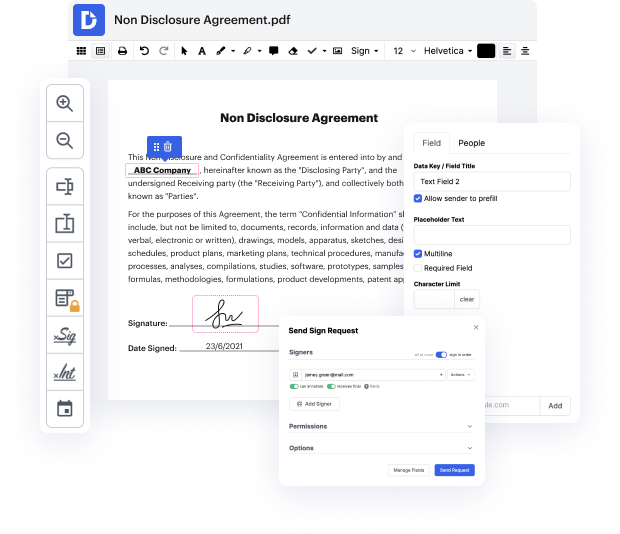
If you want to tack number in Product Evaluation with no confusion, DocHub is a perfect instrument for such duties. Our online editing platform simplifies the process for any action you may want to do with Product Evaluation. The streamlined interface is proper for any user, whether that individual is used to working with such software or has only opened it for the first time. Access all modifying tools you need easily and save your time on day-to-day editing activities. You just need a DocHub profile.
See how effortless document editing can be regardless of the document type on your hands. Access all top-notch modifying features and enjoy streamlining your work on documents. Sign up your free account now and see immediate improvements in your editing experience.
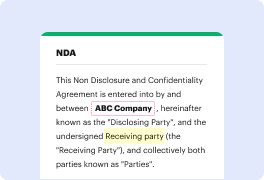
what are the mitre attack product evaluations mitre attack product evaluations show how security tools deal with real-life attack simulations based on real-life attackers the evaluations showcase security product capabilities while avoiding any scores rankings or comparisons the results can be difficult to interpret at a glance since there is no winning score so what is mitre looking for their insights can be broken down into three questions first what malicious activity to the product see and alert bomb second what relevant context was provided about the malicious activity third how fast did the products gather relevant information about the malicious activity in order to answer these questions a real-life attack is recreated using the techniques in the attack framework each step is assessed based on any of the six different detection types when the product is unable to collect any information related to malicious activity it is given a none type this is always a bad thing when the p...