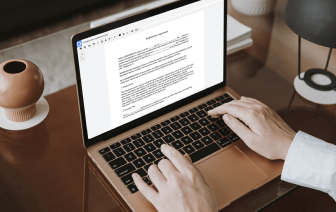
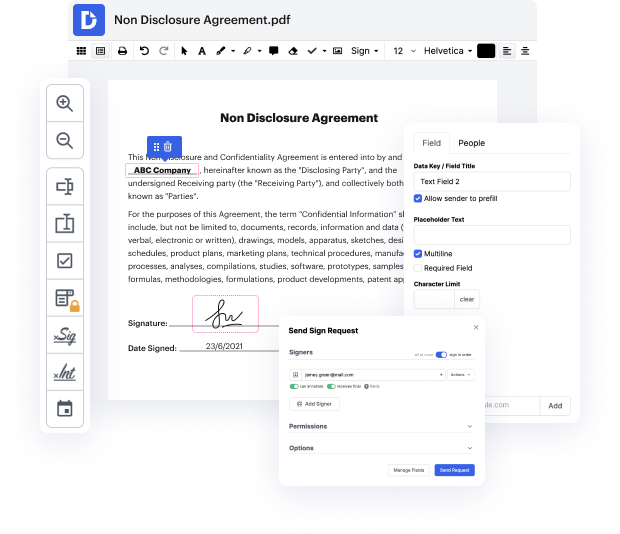
Searching for a professional tool that handles particular formats can be time-consuming. Regardless of the huge number of online editors available, not all of them support Cgi format, and certainly not all enable you to make modifications to your files. To make things worse, not all of them provide the security you need to protect your devices and documentation. DocHub is a perfect solution to these challenges.
DocHub is a popular online solution that covers all of your document editing requirements and safeguards your work with bank-level data protection. It works with different formats, such as Cgi, and allows you to modify such paperwork quickly and easily with a rich and user-friendly interface. Our tool fulfills crucial security standards, such as GDPR, CCPA, PCI DSS, and Google Security Assessment, and keeps enhancing its compliance to provide the best user experience. With everything it provides, DocHub is the most reliable way to Strike social security number in Cgi file and manage all of your individual and business documentation, regardless of how sensitive it is.
After you complete all of your alterations, you can set a password on your edited Cgi to make sure that only authorized recipients can open it. You can also save your paperwork containing a detailed Audit Trail to see who made what edits and at what time. Choose DocHub for any documentation that you need to adjust safely. Subscribe now!
hey this is David and this is an explanation of beast this ssl/tls attack and well dig right in so here is how you use the CBC mode to encrypt into the Crypt remember you have this IV and you XOR it with the plaintext when your encrypt and the ID for the next block of plaintext is actually the previous block of ciphertext so when you send your psycho types you send your IV and you need this IV this public IV to decrypt all right and there is an interesting way to use CBC in TLS 1.0 and previous versions what they would do to obtain an IV for the next message to send it wouldnt generate a new one they would instead take the previous block of ciphertext kind of like youre continuing to encrypt like its the same message except its not the same message and now the new IV for the new message is now in advance its predictable right you can just observe the message that was sent in for next message you we all know what the the IVs so this is pretty bad there is supposed to be random in