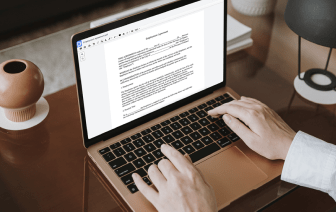
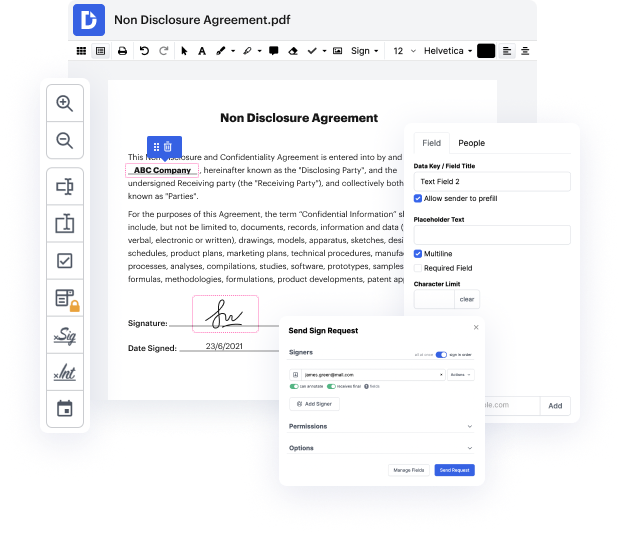
Today’s document management market is huge, so finding the right solution satisfying your needs and your price-quality expectations can be time-consuming and burdensome. There’s no need to waste time browsing the web in search of a versatile yet easy-to-use editor to Strike contents in Xml file. DocHub is here to help you whenever you need it.
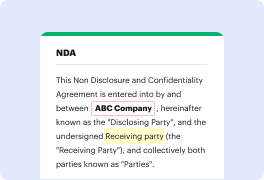
DocHub is a globally-known online document editor trusted by millions. It can satisfy almost any user’s request and meets all necessary security and compliance standards to guarantee your data is safe while modifying your Xml file. Considering its rich and straightforward interface offered at a reasonable price, DocHub is one of the most beneficial choices out there for optimized document management.
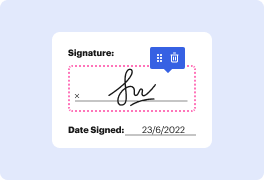
DocHub provides many other capabilities for efficient document editing. For instance, you can turn your form into a multi-use template after editing or create a template from scratch. Explore all of DocHub’s features now!
[Music] hey guys welcome back to another episode on how to hack so now were going to discuss about xxe part two all right so this is the part where we are going to try or to launch the xsd attack against the web application system so were on lesson number four of webcoat under a4 xml external entities so all were going to do right now is to look under this section all right so it says in this assignment you add a comment to the photo when submitting the form try to execute an xxc injection with the comments view try listing the root directory of the file system so the first thing we want to do is just go ahead with the normal process all right so which is to understand what happens when you go through how a normal user all right well actually input data into the system or into the database and ultimately returning as a result so we can enter for example test and i can click submit and immediately we can see over here that we have the result test so we have inputted something right