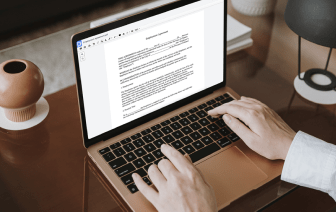
Searching for a professional tool that handles particular formats can be time-consuming. Despite the vast number of online editors available, not all of them support Xml format, and definitely not all allow you to make adjustments to your files. To make matters worse, not all of them give you the security you need to protect your devices and paperwork. DocHub is a great answer to these challenges.
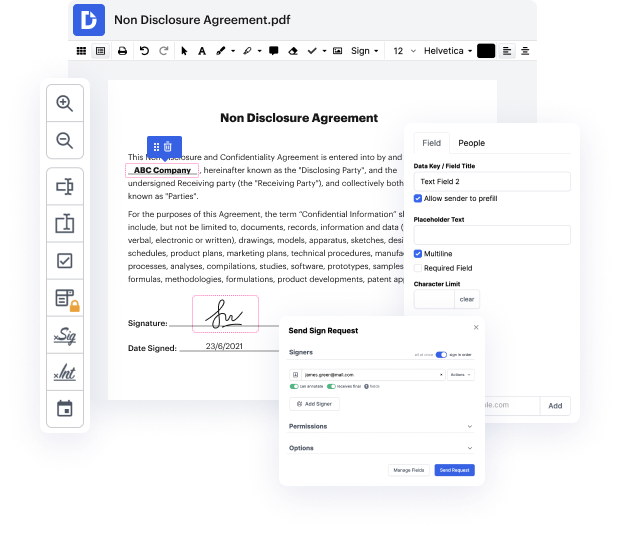
DocHub is a well-known online solution that covers all of your document editing requirements and safeguards your work with enterprise-level data protection. It works with different formats, including Xml, and enables you to edit such documents easily and quickly with a rich and intuitive interface. Our tool fulfills important security certifications, such as GDPR, CCPA, PCI DSS, and Google Security Assessment, and keeps enhancing its compliance to guarantee the best user experience. With everything it provides, DocHub is the most reputable way to Snip redline in Xml file and manage all of your individual and business paperwork, irrespective of how sensitive it is.
As soon as you complete all of your adjustments, you can set a password on your edited Xml to ensure that only authorized recipients can work with it. You can also save your paperwork containing a detailed Audit Trail to find out who made what edits and at what time. Choose DocHub for any paperwork that you need to edit safely. Subscribe now!
in this video were going to take a look at an SQL injection Challenge on portswigers web Security Academy the lab is called SQL injection with filter bypass via XML encoding and theres only a little bit of information here so let me just read through this before we jump into the lab it tells us that so far weve been using query strings to inject a malicious SQL payload however its important to note that you can perform SQL injection attacks using any controllable input thats processed as an SQL query by the application for example some websites take input in Json or XML format and use this to query the database these different formats may even provide alternative ways for you to obfuscate attacks that are otherwise block due to web application firewalls and other defense mechanisms weak implementations often just look for common SQL injection keywords within the request so you may be able to bypass these filters by simply encoding or escaping characters in The prohibited keywords