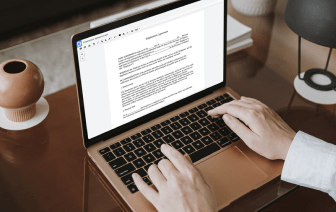
Document generation and approval certainly are a central priority for each business. Whether dealing with large bulks of documents or a particular agreement, you have to remain at the top of your efficiency. Choosing a excellent online platform that tackles your most typical file generation and approval difficulties may result in a lot of work. A lot of online platforms offer merely a restricted list of modifying and eSignature functions, some of which could possibly be valuable to deal with DOCM formatting. A solution that deals with any formatting and task might be a outstanding choice when selecting software.
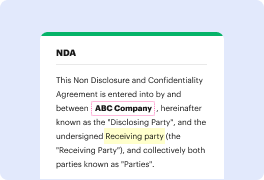
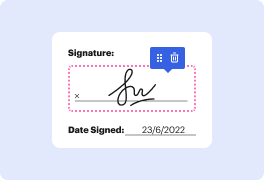
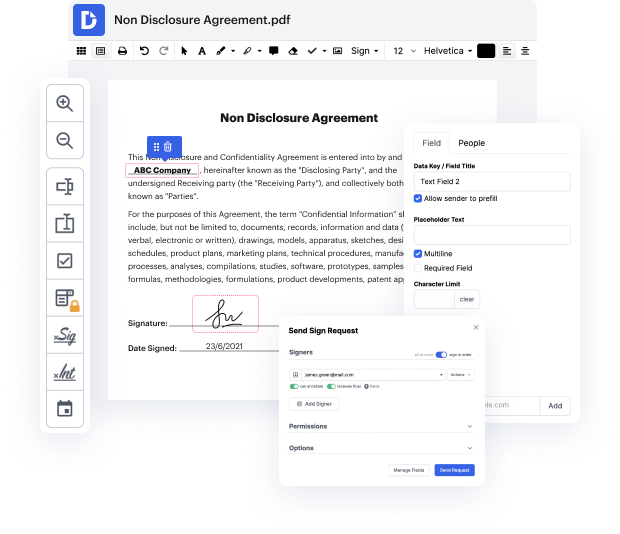
Get file administration and generation to a different level of simplicity and sophistication without opting for an awkward interface or costly subscription plan. DocHub offers you instruments and features to deal efficiently with all file types, including DOCM, and carry out tasks of any difficulty. Change, arrange, and produce reusable fillable forms without effort. Get full freedom and flexibility to set authentication in DOCM anytime and securely store all of your complete documents within your account or one of several possible incorporated cloud storage space platforms.
DocHub provides loss-free editing, signature collection, and DOCM administration on a expert levels. You do not have to go through tiresome guides and invest countless hours figuring out the application. Make top-tier safe file editing a typical process for your everyday workflows.
Many operating systems will use a feature known as directory services. This is a central database that stores usernames, passwords, computers, printers, and other devices that might be connected to the network. This database is distributed across multiple devices, and those databases will communicate to each other, and send replication data so that every database is always up to date with the latest information. This means that when a user needs to access the network, they simply use their single username and password, and those credentials are checked against this directory services database. The users only need to remember this single authentication method, and that single method generally gives you access to all of the resources you need on that network. One of the most common directory services in use is Microsofts Active Directory. We commonly use the Kerberos protocol or LDAP to be able to access that database from an external device. Instead of maintaining your own database o