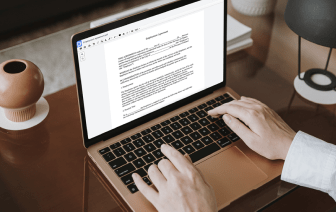
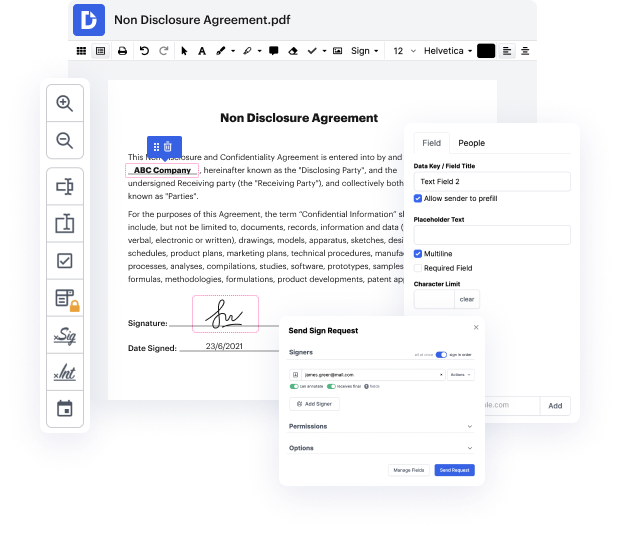
Searching for a specialized tool that deals with particular formats can be time-consuming. Regardless of the huge number of online editors available, not all of them are suitable for ODM format, and certainly not all allow you to make modifications to your files. To make things worse, not all of them give you the security you need to protect your devices and documentation. DocHub is a great answer to these challenges.
DocHub is a popular online solution that covers all of your document editing needs and safeguards your work with enterprise-level data protection. It works with various formats, including ODM, and enables you to edit such paperwork easily and quickly with a rich and intuitive interface. Our tool complies with crucial security certifications, such as GDPR, CCPA, PCI DSS, and Google Security Assessment, and keeps improving its compliance to provide the best user experience. With everything it offers, DocHub is the most reputable way to Negate token in ODM file and manage all of your individual and business documentation, no matter how sensitive it is.
Once you complete all of your modifications, you can set a password on your edited ODM to ensure that only authorized recipients can open it. You can also save your document with a detailed Audit Trail to see who made what changes and at what time. Select DocHub for any documentation that you need to edit safely. Sign up now!
user authentication there are two main ways to get the job done sessions and s the traditional approach on the web is cookie-based server-side sessions the process begins with a user filling out their username and password and then submitting it to a server which then validates it creates a session in the database then responds with a session id the session id will be saved in the browsers cookie jar which is a place in the browser to save key value pairs that will be sent back to the server on each subsequent request it can then respond back with content designed for the currently logged end user in other words we have a stateful session between the front end client and backend server this approach works great but there are some drawbacks it can be vulnerable to an attack known as cross-site request forgery where the attacker points the user to a site theyre logged into to perform actions they didnt intend to like submitting a payment or changing their password although the risk is