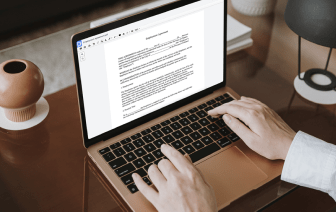
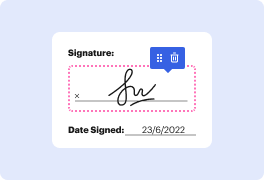
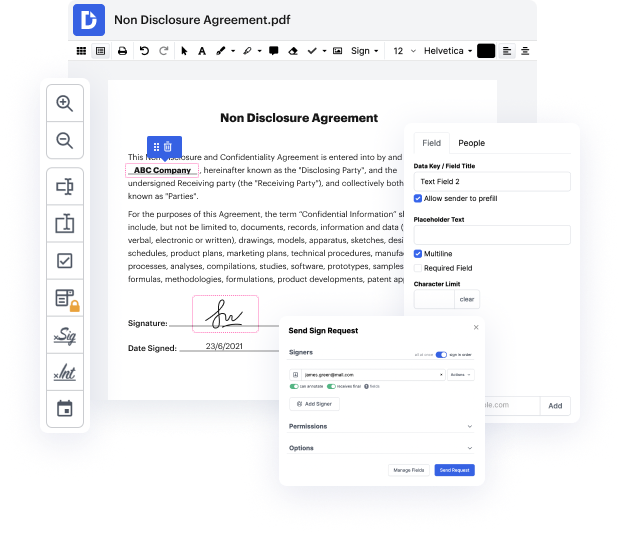
Editing image is fast and simple using DocHub. Skip installing software to your PC and make adjustments using our drag and drop document editor in a few quick steps. DocHub is more than just a PDF editor. Users praise it for its ease of use and robust features that you can use on desktop and mobile devices. You can annotate documents, create fillable forms, use eSignatures, and send documents for completion to other people. All of this, put together with a competing price, makes DocHub the perfect choice to negate authentication in image files effortlessly.
Make your next tasks even easier by converting your documents into reusable templates. Don't worry about the security of your information, as we securely keep them in the DocHub cloud.
um I would like to tell you about a recent re sorry Recent research done withan uh and the system that we built called photo prooof for authenticating images and letamp;#39;s start with some motivation uh photographic images are nowadays ubiquitous especially in the digital medium and they are used as evidence that a certain physical scene once happened in reality this happens in numerous context in the legal context as legal evidence in journalism in politics in social interactions of All Sorts whether positive or negative as in shaming or extortion it happens in dating website as proofs of physical attractiveness uh and perhaps in the most important form of images on the internet that uh frequently stretch our credulity about physics and physique cats and uh in all of these cases uh thereamp;#39;s the question of uh um is are is the claim true is the evidence really truthful and of course with the ease of digital manipulation um itamp;#39;s often false taking dating website for ex