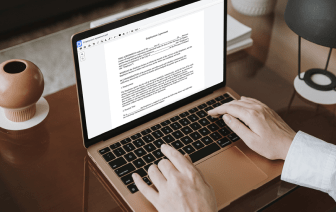
When you work with different document types like Security Proposal Template, you understand how important precision and focus on detail are. This document type has its particular structure, so it is crucial to save it with the formatting intact. For this reason, working with this sort of documents can be quite a struggle for conventional text editing software: one wrong action may mess up the format and take additional time to bring it back to normal.
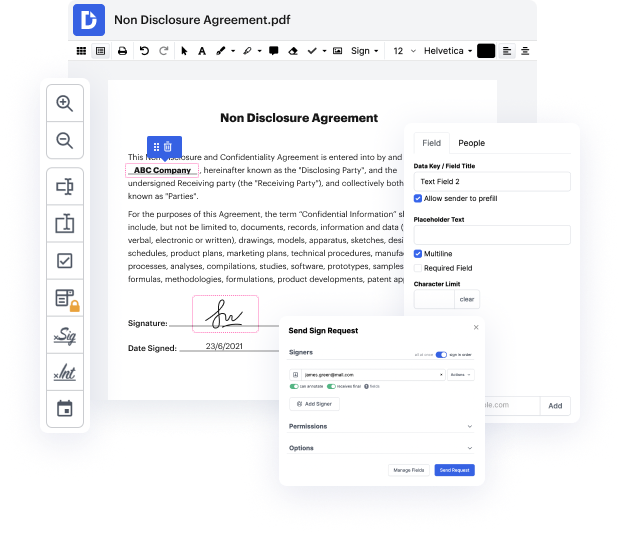
If you want to link card in Security Proposal Template with no confusion, DocHub is a perfect instrument for this kind of tasks. Our online editing platform simplifies the process for any action you may need to do with Security Proposal Template. The sleek interface design is suitable for any user, no matter if that person is used to working with this kind of software or has only opened it for the first time. Access all modifying instruments you need easily and save your time on daily editing tasks. You just need a DocHub account.
See how straightforward document editing can be irrespective of the document type on your hands. Access all top-notch modifying features and enjoy streamlining your work on paperwork. Sign up your free account now and see immediate improvements in your editing experience.
testing one two testing one two um so hey guys welcome to convo courses my name is bruce and im going to be answering a couple questions uh about risk management framework cyber security type stuff information technology anything i can answer and im starting off with uh some questions that i received on my channel here from jackie o who says are you are you able to share a complete example would you like would like to know what acceptable what an acceptable deliverable ssp looks like you mentioned youd share a copy in the section below so um so in order i i think maybe i might have mistakenly not put the link in there but if you go to convo courses i have a breakdown of how to put together an acceptable package what are all the steps that go into creating a system security plan for the nist so but what i can do for you jackie and for anybody else who is wanting to see what a system security plan looks like i can give you an example so the thing is an acceptable deliverable for an s