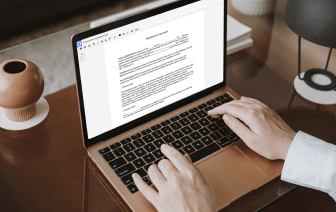
Searching for a professional tool that handles particular formats can be time-consuming. Regardless of the huge number of online editors available, not all of them are suitable for WRI format, and definitely not all allow you to make changes to your files. To make matters worse, not all of them give you the security you need to protect your devices and documentation. DocHub is an excellent answer to these challenges.
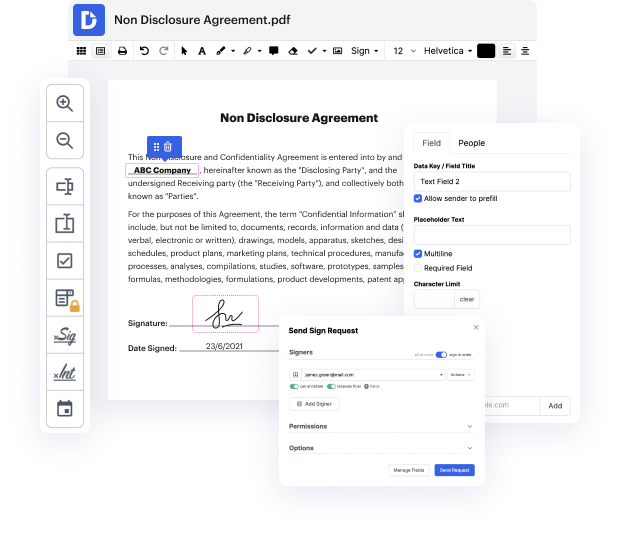
DocHub is a popular online solution that covers all of your document editing needs and safeguards your work with enterprise-level data protection. It supports different formats, including WRI, and enables you to modify such documents quickly and easily with a rich and user-friendly interface. Our tool meets essential security certifications, such as GDPR, CCPA, PCI DSS, and Google Security Assessment, and keeps improving its compliance to provide the best user experience. With everything it provides, DocHub is the most reliable way to Join authentication in WRI file and manage all of your personal and business documentation, regardless of how sensitive it is.
When you complete all of your modifications, you can set a password on your updated WRI to make sure that only authorized recipients can work with it. You can also save your paperwork containing a detailed Audit Trail to check who made what edits and at what time. Choose DocHub for any documentation that you need to edit safely. Subscribe now!
hi and welcome back to another episode on how to hack and today well be learning about how you can get access into a system without trying Brute Force attacks [Music] yes I know this sounds crazy but it can absolutely be done you just really have to understand how those applications store their passwords and credentials and all you got to do then is just to replay the password into the login field and thats it it came over and remember kids hacking is legal if you want to hack do not try to hack against hacker law because hacker law can fire IP address your password and everything about you and the reason why this can be happening is because one there is another vulnerable service within the target server and the hacker gained access over into the service and after which the hacker then go over into the listing of the photos directory and the final that okay in this particular other service there is a config folder and in a config folder they store all these different credentials lik