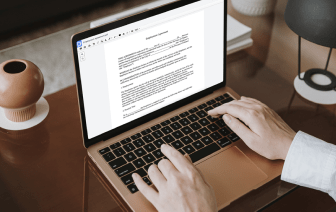
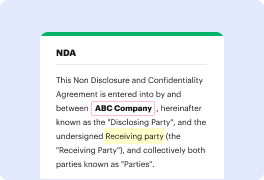
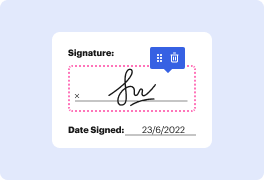
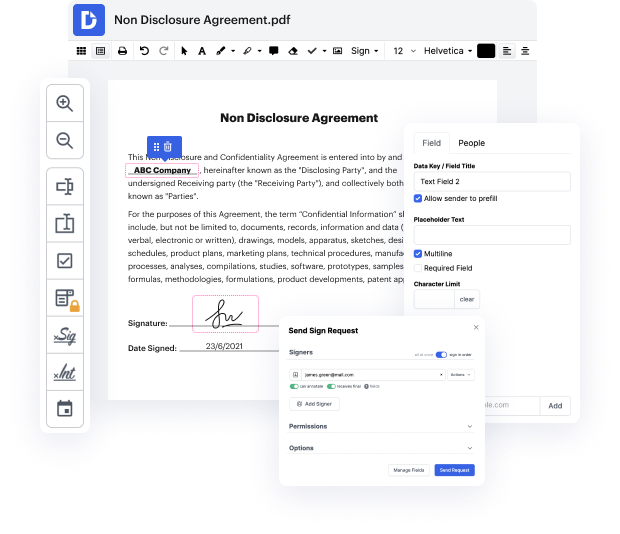
With DocHub, you can quickly inlay personal information in LOG from any place. Enjoy features like drag and drop fields, editable textual content, images, and comments. You can collect electronic signatures securely, include an extra level of protection with an Encrypted Folder, and work together with teammates in real-time through your DocHub account. Make adjustments to your LOG files online without downloading, scanning, printing or sending anything.
You can find your edited record in the Documents tab of your account. Create, email, print, or turn your file into a reusable template. With so many advanced features, it’s simple to enjoy seamless document editing and management with DocHub.
hey this is cam with Blacktail studio and this is the how to use my Blacktail Studio bowtie jig video for this you will only need a couple of things one of those things is the Blacktail Studio bowtie jig youamp;#39;ll also need a router like this one and it doesnamp;#39;t have to be an expensive one Iamp;#39;ll get to that later youamp;#39;ll need an eighth inch router bit that comes with an inlay kit or if you donamp;#39;t want to buy the inlay kit you can purchase this separately and use your own brass bushings after that youamp;#39;ll need some way to cut these out Iamp;#39;ll be using a band saw but you could probably also use a table saw and that is about it and Iamp;#39;ll show you every step to make several different designs even though thereamp;#39;s only three slots here weamp;#39;ll go through how you can actually probably more than double the number of bow tie designs you can get from this one jig itamp;#39;s important how you know an inlay jig actually works so h