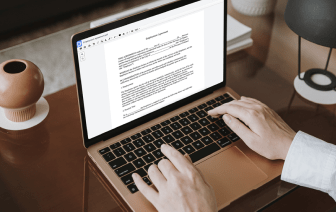
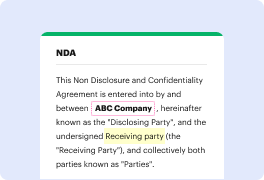
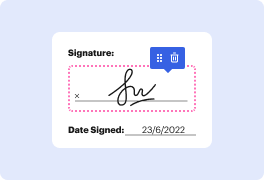
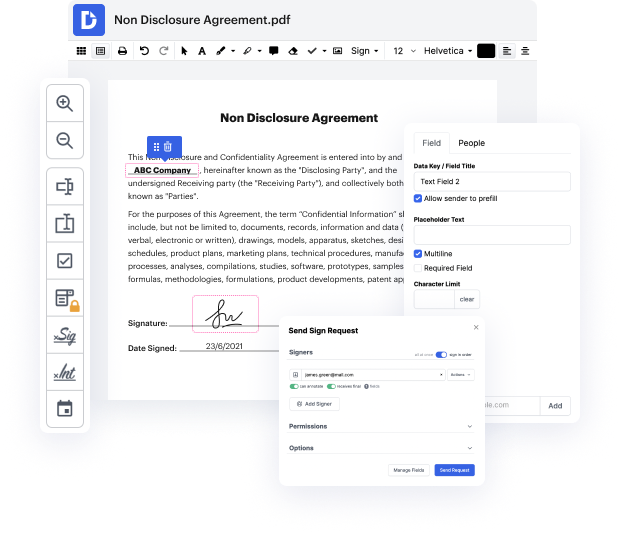
You can’t make document modifications more convenient than editing your LOG files online. With DocHub, you can get tools to edit documents in fillable PDF, LOG, or other formats: highlight, blackout, or erase document elements. Add text and pictures where you need them, rewrite your form completely, and more. You can save your edited record to your device or share it by email or direct link. You can also transform your documents into fillable forms and ask others to complete them. DocHub even provides an eSignature that allows you to certify and send paperwork for signing with just a few clicks.
Your records are safely kept in our DocHub cloud, so you can access them at any time from your desktop, laptop, smartphone, or tablet. Should you prefer to apply your mobile phone for file editing, you can easily do it with DocHub’s app for iOS or Android.
whatamp;#39;s going on guys welcome back in todayamp;#39;s video weamp;#39;re going to talk about logging in python so let us get right into it all right so letamp;#39;s talk about logging i think logging is one of those things that people oftentimes donamp;#39;t want to do a little bit like testing because itamp;#39;s a little bit boring itamp;#39;s not the most fancy thing not the most interesting thing that you can do in coding but itamp;#39;s one of those things that save you a lot of time and can help you tremendously if you need them now you hope you wonamp;#39;t need them but if you need them you have a lot of data to analyze for example letamp;#39;s say your program crashes or your service doesnamp;#39;t work anymore you can look into the logs into the past logs into the current locks to see what is going on or what was going on what caused the problem what is the core of the problem and how can we find a solution so logging is something uh that is a long-ter