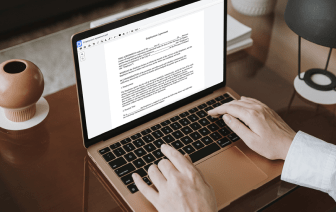
Whether you are already used to dealing with CWK or managing this format for the first time, editing it should not feel like a challenge. Different formats may require specific software to open and modify them effectively. Nevertheless, if you need to quickly inject line in CWK as a part of your usual process, it is best to get a document multitool that allows for all types of such operations without extra effort.
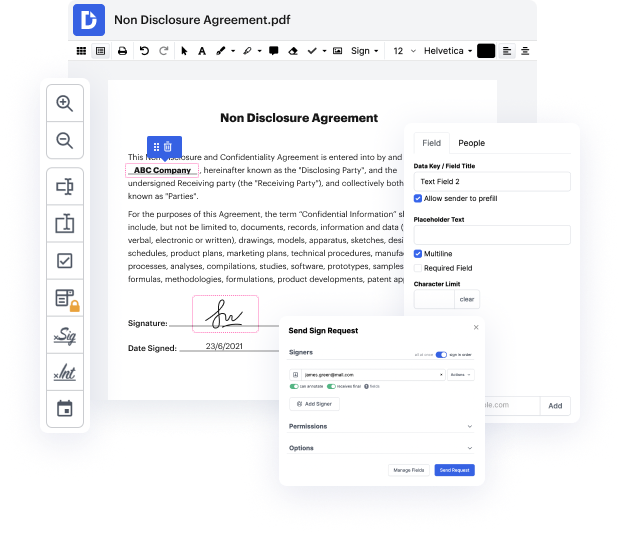
Try DocHub for efficient editing of CWK and other document formats. Our platform offers straightforward papers processing no matter how much or little previous experience you have. With all instruments you have to work in any format, you will not have to jump between editing windows when working with every one of your documents. Effortlessly create, edit, annotate and share your documents to save time on minor editing tasks. You will just need to sign up a new DocHub account, and then you can start your work instantly.
See an improvement in document processing efficiency with DocHub’s simple feature set. Edit any document quickly and easily, regardless of its format. Enjoy all the benefits that come from our platform’s simplicity and convenience.
hello everybody and welcome back to another video in todays hacker tools episode we will be looking at crlf fuzz a tool where you can inject new lines and get bounties [Music] a crlf injection is the injection of a new line or a cscrlf so carriage return line feed in places where the server doesnt expect them then that can cause a multitude of vulnerabilities such as xss session fixation cookie injection open redirects and so on so what are we waiting for lets take a look at crlf first in my kali machine here i have a vulnerable website up and running and it has a endpoint slash version one and slash test and if i send that request in burp we will see that the response by the server contains this header x dash action is equal to test now that seems to be the text that we submitted as the endpoint in our get request so lets try changing tests to for example integrity and then if we resend that request well we see that x-action that header now contains the value integrity okay so we