Safety should be the primary consideration when looking for a document editor on the web. There’s no need to waste time browsing for a trustworthy yet cost-effective service with enough capabilities to Inject code in Retirement Plan. DocHub is just the one you need!
Our solution takes user privacy and data protection into account. It complies with industry standards, like GDPR, CCPA, and PCI DSS, and constantly extends compliance to become even more hazard-free for your sensitive information. DocHub allows you to set up two-factor authentication for your account settings (via email, Authenticator App, or Backup codes).
Therefore, you can manage any paperwork, such as the Retirement Plan, absolutely securely and without hassles.
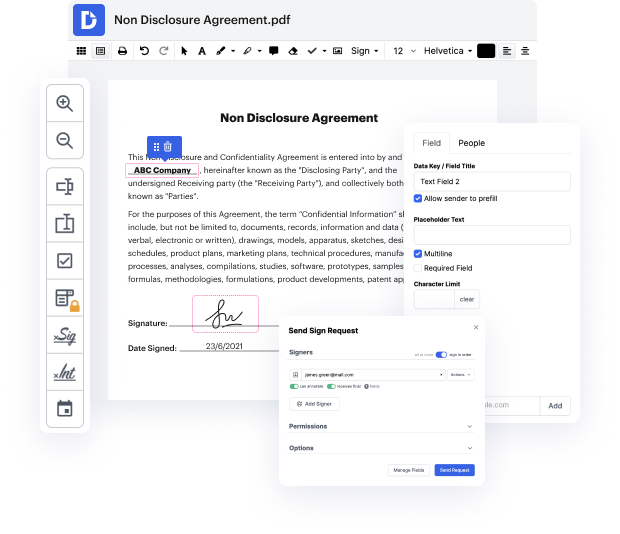
Apart from being trustworthy, our editor is also very simple to work with. Follow the guideline below and make sure that managing Retirement Plan with our tool will take only a couple of clicks.
If you frequently manage your paperwork in Google Docs or need to sign attachments you’ve got in Gmail rapidly, DocHub is also a good option to choose, as it perfectly integrates with Google services. Make a one-click file import to our editor and accomplish tasks within minutes instead of continuously downloading and re-uploading your document for processing. Try out DocHub today!
[Music] so what are some things that 40 year olds should consider well assuming you have the insurance and the you know emergency savings we talked about in the 30s 40s is one of the early you know first times in your life where your income is really starting to increase you have a great opportunity to start maxing out various plans investing as much as you can but it can also be a challenge because thats when your kids are often hitting the more expensive club years or whatever else things theyre doing and saving for college et cetera so um theres a lot of conflict in the 40s yeah you know it seems like theres conflicts every year but 40s in particular as the kids get older yeah absolutely we both have experience we have experienced that so lets go over an example of of someone in their 40s to continue our example so someone that has 210 000 dollars to start and their lets say their salary now goes up to 110 000 they would need to save 13.75 at a 7 rate of return to end up with
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



