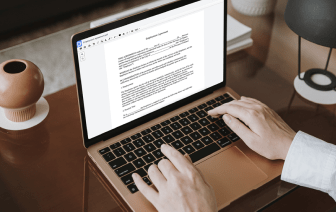
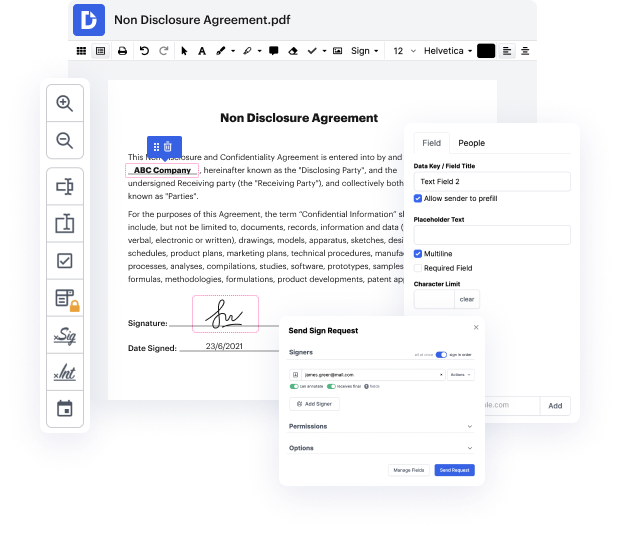
At the first blush, it may seem that online editors are very similar, but you’ll realize that it’s not that way at all. Having a powerful document management solution like DocHub, you can do much more than with regular tools. What makes our editor exclusive is its ability not only to quickly Inject code in Privacy Policy but also to create documentation totally from scratch, just the way you want it!
Regardless of its comprehensive editing features, DocHub has a very easy-to-use interface that offers all the features you need at hand. Thus, modifying a Privacy Policy or a completely new document will take only a few minutes.
Sign up for a free trial and celebrate your greatest-ever document-related practice with DocHub!
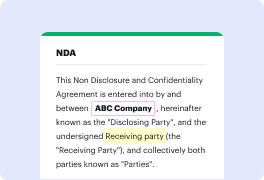
at some point while publishing an app you may need to link your privacy policy lets quickly generate it go to this link provided in the video description you will need to fill out some details name of your app contact information what kind of data you will be collecting like nickname IP address email names and more then select if your app is free or paid what is your target platform are you an individual or a company and finally what is your name then click next and select what kind of services are you using in your product for example if you are integrating admob and Facebook SDK simply select those options then click next and were done under privacy policy you can find a fully generated text now time to publish it select the whole policy and copy it then go to sites.google.com and click new blank site rename the header to privacy policy enter site name for example the name of your app and finally add a new text box with pasted content from the generator here it is to publish it cli