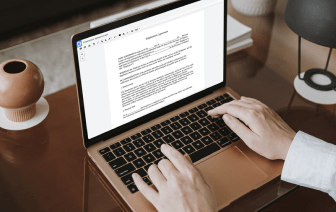
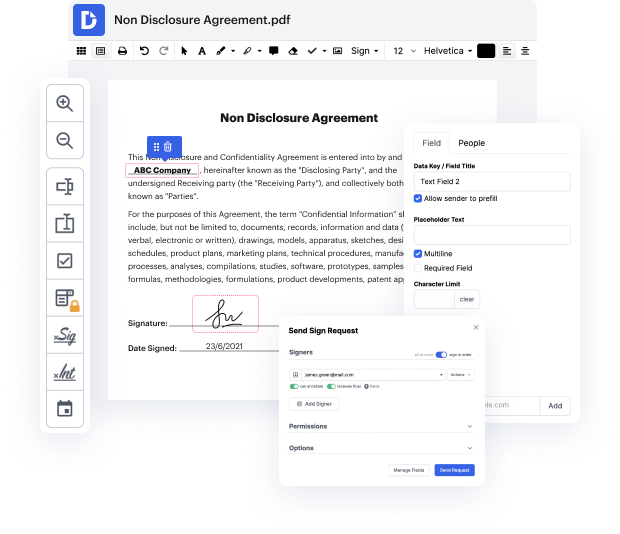
DocHub is an all-in-one PDF editor that allows you to inject authentication in NEIS, and much more. You can highlight, blackout, or remove document fragments, insert text and pictures where you want them, and collect data and signatures. And because it works on any web browser, you won’t need to update your device to access its robust features, saving you money. When you have DocHub, a web browser is all you need to handle your NEIS.
Sign in to our website and adhere to these guidelines:
It couldn't be easier! Enhance your document processing today with DocHub!
[Applause] hello everybody welcome back to another episode of rethinking connectivity my name is jeremy and today weamp;#39;re going to be going over the authentication and authorization model inside of nats essentially our security model now this is a really big topic to cover but i figured weamp;#39;ve gotten a lot of requests for us to cover it so today weamp;#39;re going to dive in deep and iamp;#39;m going to go over the overall architecture and some of the design choices that we made around building a security model like this and then weamp;#39;re going to dive in and weamp;#39;re going to actually sketch one out iamp;#39;m using a tool called nsc and applying it to our nat server and i could show you all the different ways that you can kind of lock down certain accounts that you could share between accounts etc etc so letamp;#39;s dive straight in so what is what is it that we call decentralized off often and off z and gnats well itamp;#39;s a couple of