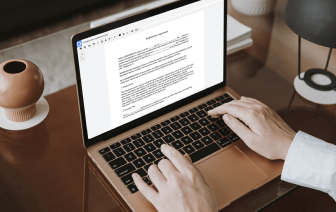
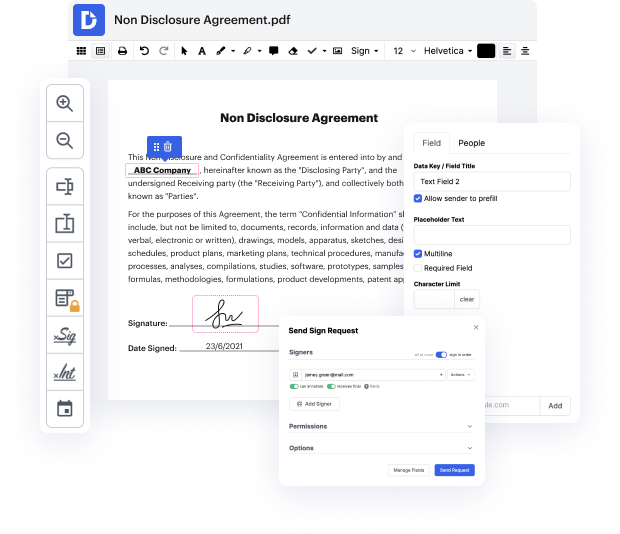
Many people find the process to inject authentication in image rather challenging, especially if they don't frequently deal with paperwork. Nonetheless, nowadays, you no longer have to suffer through long instructions or wait hours for the editing software to install. DocHub lets you change forms on their web browser without installing new applications. What's more, our robust service offers a full set of tools for professional document management, unlike numerous other online tools. That’s right. You no longer have to donwload and re-upload your forms so frequently - you can do it all in one go!
Whatever type of document you need to adjust, the process is simple. Make the most of our professional online solution with DocHub!
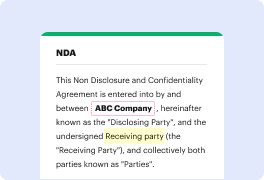
building graphical password by image segmentation this is a.net based project with an MS SQL database we have the source code open in Visual Studio letamp;#39;s get started with the project the user will need to register first to log into the system to set a graphical password an image needs to be selected the system will segment the uploaded image into an array of images and store them again the user will need to log in they will need to log in using their email ID and password the user will need to enter the correct image pattern the jumbled image must be sorted and numbered in an order that matches the original image sorting of images must be started from the top left corner onwards the user is granted access after a successful attempt our graphical password system using image segmentation allows users to input an image and set it as a graphical password and only the user knows what the original image looks like and please do not forget to like share and subscribe also hit the a be