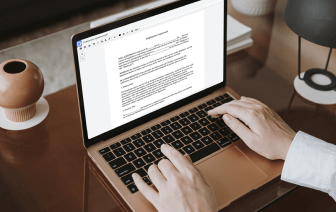
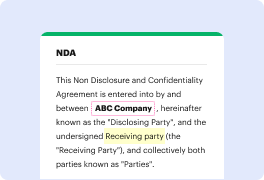
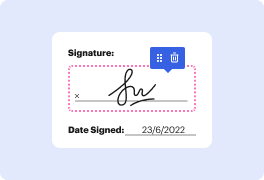
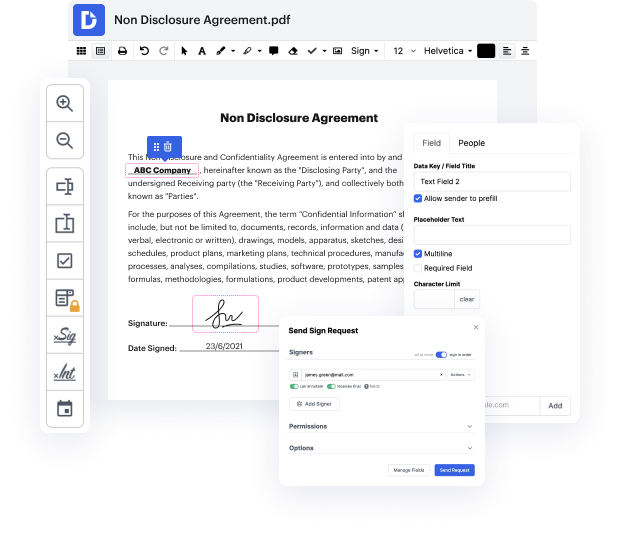
With DocHub, you can quickly inject authentication in cgi from anywhere. Enjoy capabilities like drag and drop fields, editable textual content, images, and comments. You can collect electronic signatures securely, include an additional layer of defense with an Encrypted Folder, and work together with teammates in real-time through your DocHub account. Make changes to your cgi files online without downloading, scanning, printing or mailing anything.
You can find your edited record in the Documents tab of your account. Edit, send, print, or turn your file into a reusable template. With so many powerful tools, it’s easy to enjoy seamless document editing and management with DocHub.
hello my name is Micah Silverman I am a senior security hacks or for octa I work on our developer advocacy team and today I want to talk to you about a particular Roth attack called the authorization code injection attack now Iamp;#39;m not going to go into a lot of detail about OAuth and the various flows I will make sure to have a bunch of links down in the comments to get the introductory stuff if youamp;#39;re new to oh oh ah thereamp;#39;s been a lot of conversation in the OAuth working group about mandating the pixi extension even for confidential clients and so thatamp;#39;s why I thought it would be interesting to put together a practical example of this exploit and how pixie defeats it the authorization code flow for confidential clients has long been considered the most secure flow that there is and that is still true but pixie adds an extra degree of protection as weamp;#39;ll see if youamp;#39;re familiar with OAuth and the authorization code flow you know tha