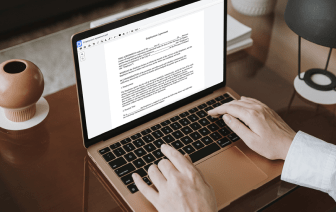
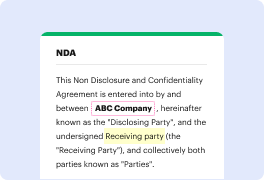
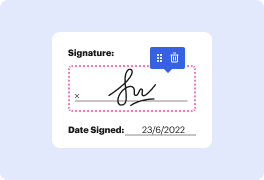
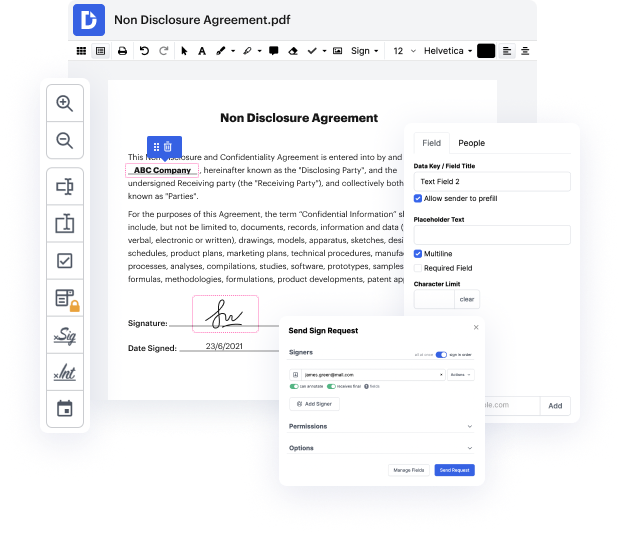
DocHub makes it fast and simple to inject address in LOG. No need to instal any software – simply upload your LOG to your account, use the easy drag-and-drop user interface, and quickly make edits. You can even use your computer or mobile device to adjust your document online from any place. That's not all; DocHub is more than just an editor. It's an all-in-one document management solution with form creating, eSignature capabilities, and the ability to enable others fill in and eSign documents.
Each file you upload you can find in your Documents folder. Create folders and organize records for easier search and retrieval. In addition, DocHub guarantees the safety of all its users' information by complying with stringent protection standards.
now Iamp;#39;m riding the one welcome back to explain today weamp;#39;re going to have a look at the login benda and challenge and the scripture is relatively short right now it only says login with benders user account and we know that in order to login we have to go up here account and click on login and standing at the email address and password field first of all we have to figure out what the email address of bender is and if we do not know that by now we can just refresh the page and look at verb and we do see that there is a rest and point called rest admin application configuration and if we look at the response there is a domain in here right here which says juice more thatamp;#39;s SH dot o P and thatamp;#39;s thatamp;#39;s actually the domain used for all the email addresses and if youamp;#39;ve been following along this playlist you have seen a couple of other email addresses that weamp;#39;ve seen before so we know anyway that this is what we are going with and to l