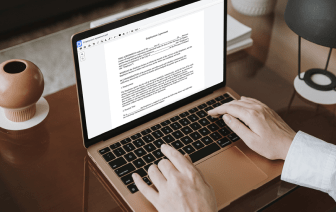
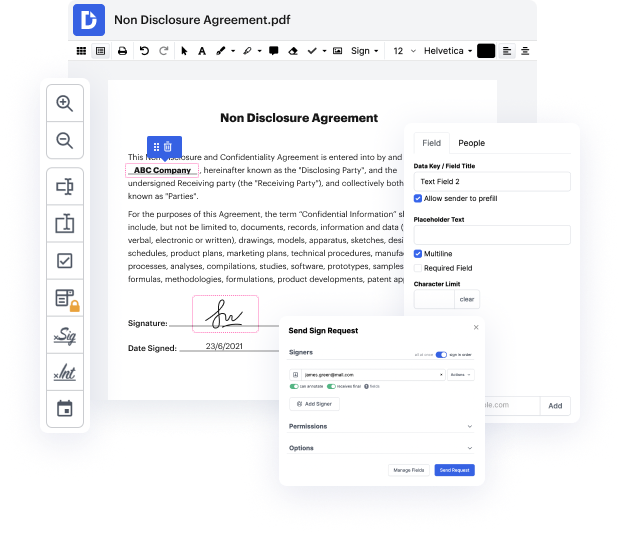
Time is a crucial resource that every organization treasures and tries to convert into a benefit. When picking document management software program, be aware of a clutterless and user-friendly interface that empowers consumers. DocHub provides cutting-edge features to maximize your file administration and transforms your PDF editing into a matter of a single click. Hide Words in the Security Agreement with DocHub to save a lot of efforts and increase your efficiency.
Make PDF editing an simple and easy intuitive operation that helps save you plenty of precious time. Easily modify your files and send them for signing without the need of turning to third-party options. Give attention to pertinent tasks and improve your file administration with DocHub starting today.
a general security agreement or a GSA is the most common form of personal property security used to secure commercial loans and other business obligations owed to a financial institution or another creditor which is a secured party such as a franchise or a GSA will secure any type of present or future obligation including loans and guarantees and rights under a franchise agreement of the party who signs the GSA who is called the debtor youll likely to find the following details in a GSA the debtors representations warranties and covenants a description of the personal property assets secured by the GSA the terms and conditions of the GSA and the enforcement rights in the event of defaults ie where the promise monies are not repaid Jesus As are most often secured over the company which is borrowing the funds or committing to an agreement like a franchise agreement however partnerships cooperatives and even individuals can also give GSA security its critical to ensure that the name on