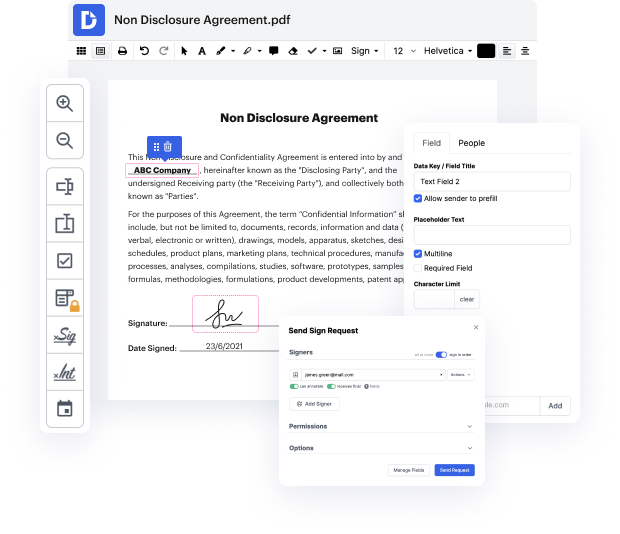
Having full control over your papers at any moment is important to alleviate your everyday tasks and improve your productivity. Accomplish any goal with DocHub features for papers management and hassle-free PDF file editing. Access, change and save and incorporate your workflows along with other secure cloud storage.
DocHub offers you lossless editing, the chance to work with any format, and securely eSign papers without looking for a third-party eSignature option. Maximum benefit from the file management solutions in one place. Consider all DocHub features today with the free profile.
In this video tutorial, Stuart Ferguson discusses the importance of well-structured maintenance work orders as the backbone of maintenance operations. He outlines six key steps for creating an effective work order, emphasizing that these documents function as vital communication tools that facilitate repair and inspection tasks. Work orders help maintenance teams organize, assign, prioritize, track, and efficiently complete tasks. Each work order follows a lifecycle, beginning with identifying necessary actions—planned maintenance can be prepared in advance, while reactive tasks are addressed as needed. The tutorial aims to enhance the understanding and effectiveness of work orders in maintenance management.
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



