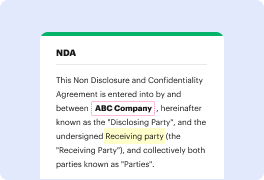
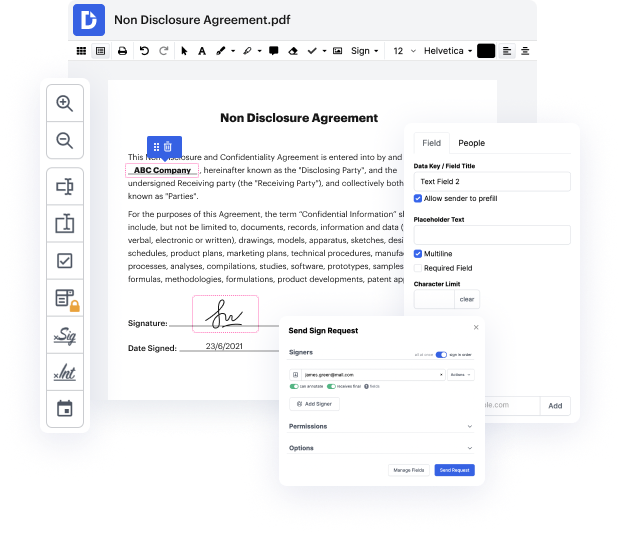
Having full control of your documents at any time is important to relieve your daily tasks and boost your efficiency. Accomplish any goal with DocHub tools for document management and practical PDF editing. Gain access, change and save and incorporate your workflows along with other secure cloud storage.
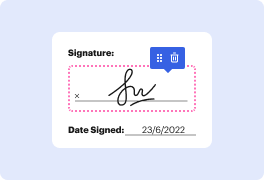
DocHub offers you lossless editing, the opportunity to work with any formatting, and securely eSign papers without the need of searching for a third-party eSignature alternative. Maximum benefit from the file management solutions in one place. Check out all DocHub functions right now with your free of charge account.
In this tutorial, Carla from ReQtest explains how to effectively fill out a bug report. A well-structured bug report facilitates quicker fixes. Key elements to include are: 1. Location details of the bug, specifying the product, version, and module.2. Information about your system, such as the platform, operating system, and browser.3. A concise title that identifies the bug, followed by a detailed description of the issue.4. An assessment of the bug's importance, indicating how urgently it needs to be addressed.By balancing the amount of information provided, you can create a report that aids in resolving bugs without unnecessary complications.