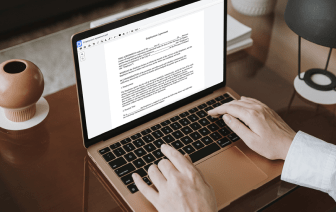
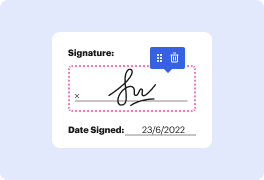
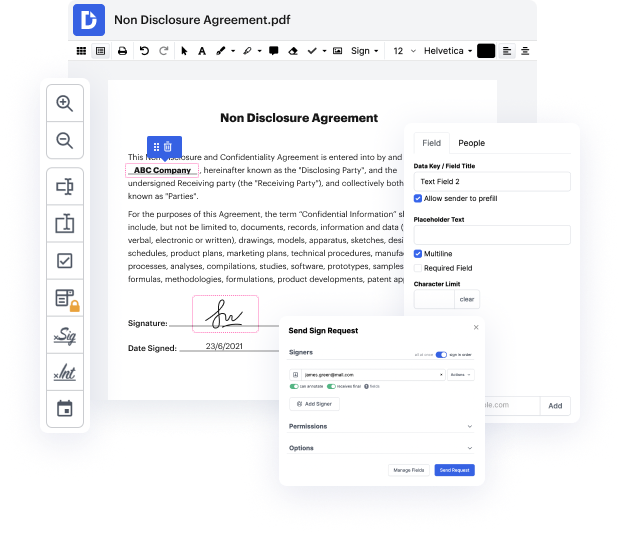
Regardless of how complex and challenging to edit your files are, DocHub offers an easy way to modify them. You can alter any part in your LOG with no effort. Whether you need to fine-tune a single component or the entire form, you can entrust this task to our powerful tool for quick and quality outcomes.
Moreover, it makes certain that the final document is always ready to use so that you’ll be able to get on with your projects without any delays. Our comprehensive set of capabilities also features sophisticated productivity tools and a catalog of templates, enabling you to make best use of your workflows without the need of losing time on routine activities. In addition, you can gain access to your documents from any device and incorporate DocHub with other solutions.
DocHub can take care of any of your form management activities. With an abundance of capabilities, you can create and export papers however you prefer. Everything you export to DocHub’s editor will be stored safely as much time as you need, with strict security and data protection frameworks in place.
Try out DocHub today and make handling your documents easier!
you can clean out your closets and your drawers all day long but if the habits that got you there are not broken you will continue to do it over and over again and for me the biggest mindset shift that helped me is when I started practicing contentment and when I really said hey with what I have Iamp;#39;m good with who I am is not going to change because of that purchase or this over here this piece that I have in my heart thereamp;#39;s like this level of foundation there you guys that is so huge cuz money can be really emotional and understanding and learning the hard way that money and buying stuff is not always going to make you happy even though we can believe that letamp;#39;s be real though