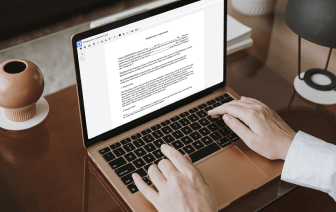
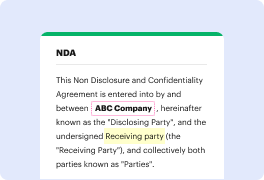
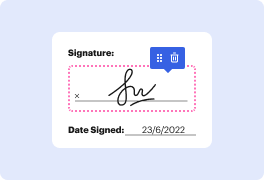
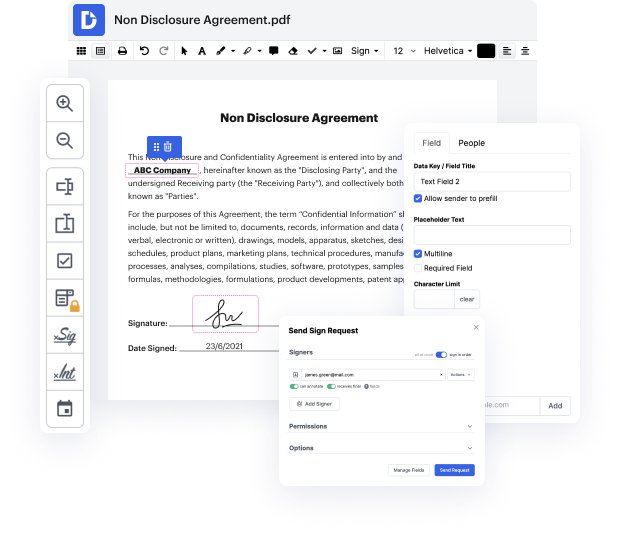
DocHub makes it fast and straightforward to cover up authentication in image. No need to download any extra application – simply upload your image to your account, use the easy drag-and-drop user interface, and quickly make edits. You can even work on your PC or mobile device to modify your document online from any place. That's not all; DocHub is more than just an editor. It's an all-in-one document management platform with form creating, eSignature features, and the ability to let others fill out and sign documents.
Each file you upload you can find in your Documents folder. Create folders and organize records for easier search and access. In addition, DocHub ensures the security of all its users' data by complying with strict security protocols.
hello and welcome back to The Nest Palm my name is Brian and today weamp;#39;re going to explore cosine a fantastic tool for signing and verifying container images to improve the security of your deployments I will guide you through the process of sending an image verifying it and even working with software bill of materials using cosine letamp;#39;s Dive In so cosine is a project developed by the cloud native Computing foundationamp;#39;s project called sigstore it is designed to provide cryptographic signing and verification for container images ensuring that they are authentic unmodified and come from a trusted Source before deployment first letamp;#39;s cosine assuming that you have the go command line tool and language installed then go github.com Sig store cosine CMD slash cosign at latest this will put the binary in gopath slash bin so we can find that by doing LS go and go path that Iamp;#39;ve been and as you can see itamp;#39;s right there now that we have cosine instal