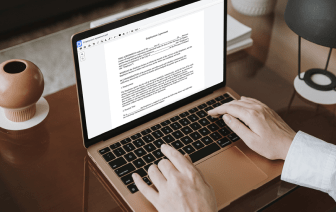
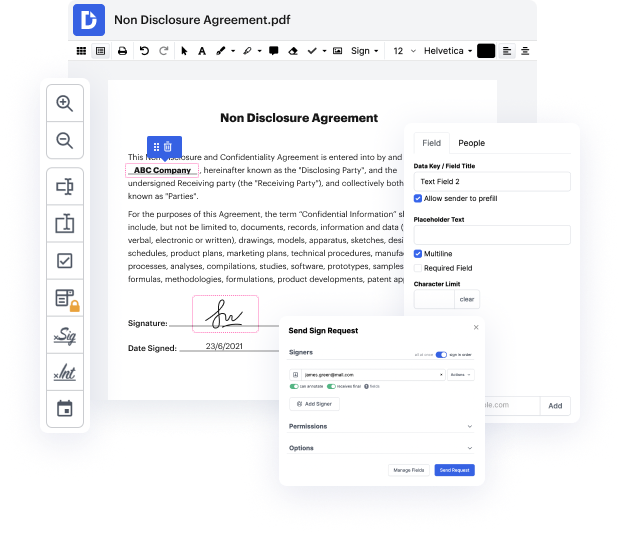
Document generation and approval are a central focus of each firm. Whether dealing with sizeable bulks of documents or a distinct agreement, you have to stay at the top of your productivity. Getting a excellent online platform that tackles your most frequentl papers creation and approval difficulties might result in quite a lot of work. Numerous online apps offer you merely a restricted set of modifying and signature functions, some of which might be useful to deal with LOG file format. A platform that handles any file format and task will be a outstanding option when picking application.
Take document administration and creation to a different level of straightforwardness and excellence without picking an awkward interface or pricey subscription plan. DocHub offers you instruments and features to deal effectively with all of document types, including LOG, and perform tasks of any complexity. Edit, arrange, and make reusable fillable forms without effort. Get total freedom and flexibility to correct phone in LOG anytime and safely store all of your complete files within your user profile or one of many possible incorporated cloud storage space apps.
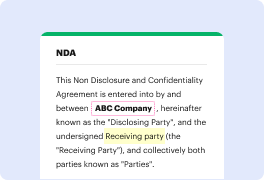
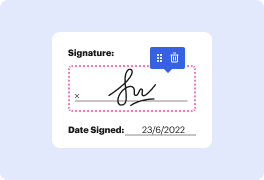
DocHub offers loss-free editing, signature collection, and LOG administration on the professional levels. You don’t need to go through tedious tutorials and invest countless hours finding out the software. Make top-tier secure document editing a standard process for your every day workflows.
- Are you concerned that your phone has recently been hacked? Heres how to tell. First, lets talk about how phones actually do get hacked. - Have you ever been in a hotel room and a nice lady comes in, tries to clean it for you? Well, guess what? Could be an evil maid. - Evil maid attack, that is when somebody has access to your physical device and they alter it in some sort of undetectable way and then they can access that data later, called the evil maid attack because it was coined after hotel room. We leave our electronics unattended at hotels and a maid- - Well, you do. - An evil maid could come in and access it. - And hack it. - Yeah. - Indeed. - Also quite common phishing scams. We get a ton of emails from people who say I just got this really weird mail from Apple. It says its from Apple, but there are all these typos and the email address is something thats not Apple. And theyre like, is this actually legit? - Right. Or a text message, same deal. I think its amazing tha