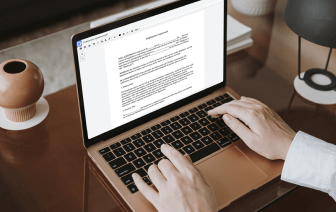
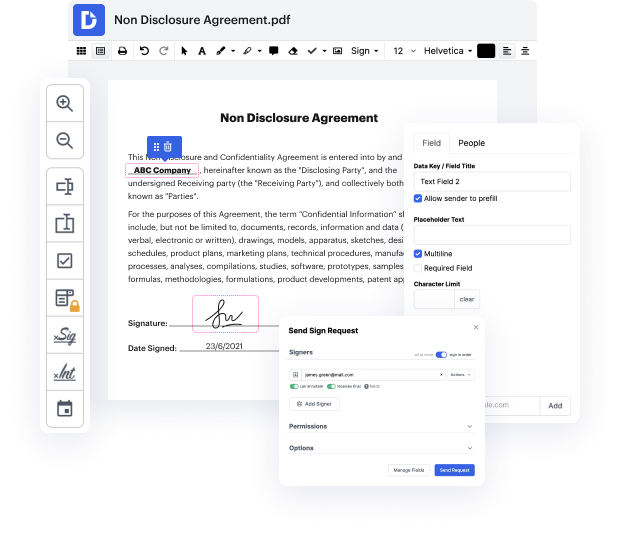
Many people find the process to conceal trace in LWP quite difficult, particularly if they don't frequently work with documents. Nevertheless, nowadays, you no longer have to suffer through long instructions or spend hours waiting for the editing app to install. DocHub enables you to change forms on their web browser without setting up new programs. What's more, our feature-rich service provides a complete set of tools for professional document management, unlike numerous other online tools. That’s right. You no longer have to export and import your forms so frequently - you can do it all in one go!
Whatever type of document you need to modify, the process is easy. Take advantage of our professional online solution with DocHub!
hi iamp;#39;m jared from lacework and today weamp;#39;re going to take a look at some shared object files that lacework labs the security research team at lacework found letamp;#39;s get started if youamp;#39;re unfamiliar a shared object file or so is typically used to provide additional functionality to other executables via exports those coming from the windows world can think of this like a dll if we take a look at the diagram we can see that with normal execution flow the binary headers are parsed memory is allocated and then in the case of dynamically linked executables the legitimate shared objects or libraries are loaded and execution is continued however by leveraging the ld preload path environment variable we can say hey program load libraries from this directory first and then continue on with normal execution this allows an adversary to have their program overload legitimate functionality provided by other shared objects and is commonly seen in both defense evasion as