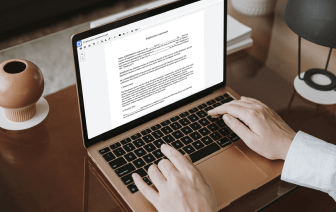
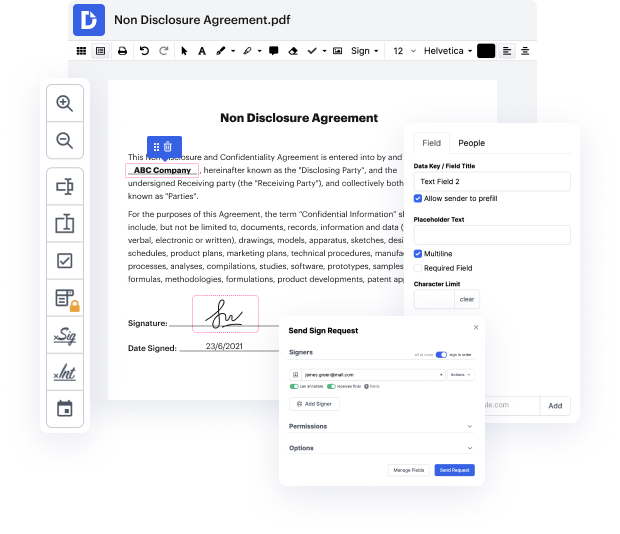
DocHub is an all-in-one PDF editor that lets you conceal issue in LOG, and much more. You can highlight, blackout, or remove document elements, insert text and pictures where you need them, and collect information and signatures. And since it works on any web browser, you won’t need to update your hardware to access its professional capabilities, saving you money. With DocHub, a web browser is all it takes to make changes in your LOG.
Log in to our website and adhere to these instructions:
It couldn't be simpler! Streamline your document processing today with DocHub!
hey guys Roland Jones how you doing uh a lot of folks have been asking me about accuracy jurisdiction especially foreign defendants but even uh potential defendants in the United States so I wanted to explain how this works a little bit so that you have a concept and youamp;#39;re better able to work with your Council uh whoever that is uh so again we donamp;#39;t have an attorney-client relationship unless you have a signed retention agreement with me donamp;#39;t act on anything you hear in this in this video Donamp;#39;t not act on any refrain from acting another thing you hear and this isnamp;#39;t just boilerplate you need a lawyer and why is that because Iamp;#39;m talking about general principles um that you can find in a book not applied to your particular case and thatamp;#39;s where the lawyering comes in the lawyering is about taking the principles and applying them to your specific fact pattern obviously Iamp;#39;m not doing that you need to hire a council to do tha