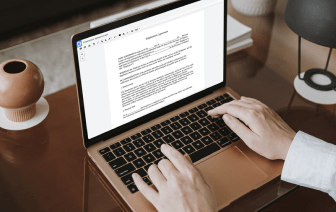
Document generation and approval certainly are a key priority for each firm. Whether dealing with large bulks of files or a distinct agreement, you must stay at the top of your efficiency. Finding a ideal online platform that tackles your most frequentl record creation and approval difficulties might result in a lot of work. Numerous online apps provide just a limited set of editing and eSignature features, some of which may be beneficial to deal with UOF format. A platform that deals with any format and task would be a outstanding choice when picking program.
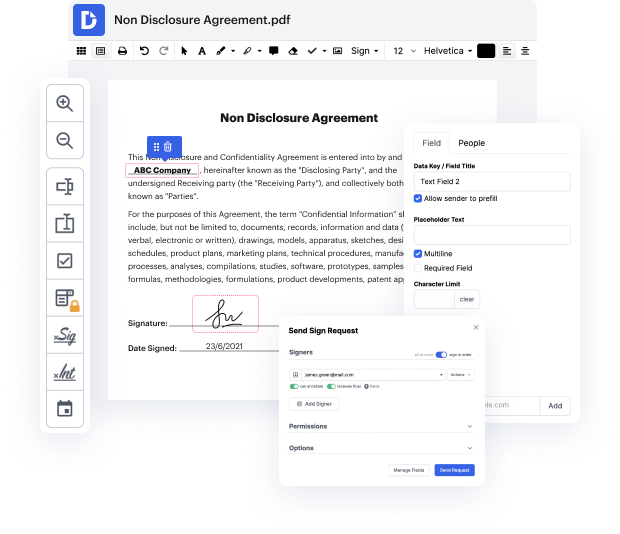
Get file managing and creation to another level of straightforwardness and excellence without opting for an cumbersome user interface or pricey subscription options. DocHub provides you with instruments and features to deal successfully with all of file types, including UOF, and perform tasks of any complexity. Change, organize, and produce reusable fillable forms without effort. Get total freedom and flexibility to clean token in UOF at any time and securely store all your complete files within your profile or one of many possible integrated cloud storage space apps.
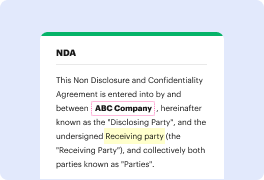
DocHub offers loss-free editing, eSignaturel collection, and UOF managing on a professional levels. You do not need to go through exhausting guides and spend a lot of time finding out the software. Make top-tier safe file editing a regular process for the daily workflows.
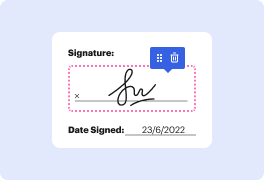
want to know more about refresh tokens and how to store them securely then keep watching this video because Ill be covering both topics [Music] hey everyone Im will Im a developer advocate here at off zero in this video Im going to talk about refresh tokens as they are defined in oauth 2.0 youll learn about how refresh tokens compare against the other two types and how they balance security usability and privacy but first lets talk about what is a what is a tokens are pieces of data with just enough information to carry out the process of determining the users Identity or authorizing the user to perform an action tokens are artifacts that allow applications to perform the authorization and authentication processes some identity Frameworks and protocols use -based strategies to secure access to applications and resources for example we use oauth 2.0 for authorization and openid connect for Authentication oauth 2.0 allows an application to access resources