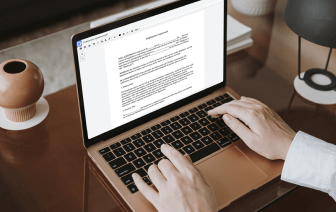
Document generation and approval certainly are a core priority of each organization. Whether working with sizeable bulks of files or a certain contract, you should stay at the top of your productivity. Choosing a perfect online platform that tackles your most frequentl file creation and approval obstacles could result in a lot of work. Numerous online platforms offer only a restricted set of editing and eSignature functions, some of which might be beneficial to deal with ACL format. A solution that deals with any format and task would be a outstanding option when deciding on application.
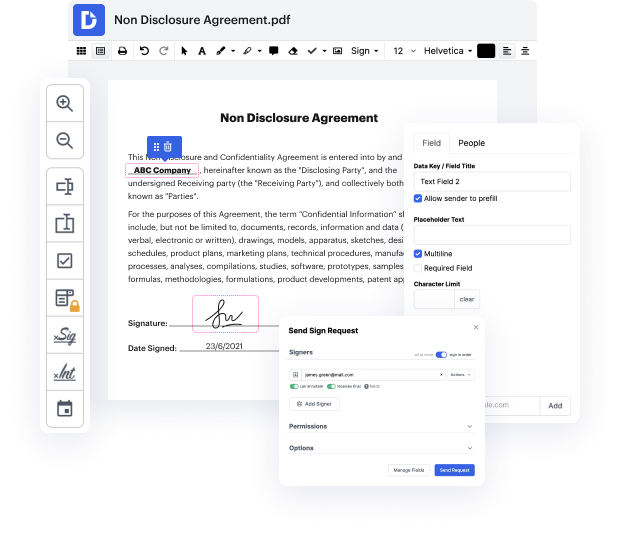
Get document managing and creation to another level of efficiency and sophistication without picking an cumbersome user interface or high-priced subscription plan. DocHub gives you tools and features to deal effectively with all document types, including ACL, and execute tasks of any complexity. Change, manage, and produce reusable fillable forms without effort. Get full freedom and flexibility to bold address in ACL at any time and securely store all of your complete documents within your profile or one of many possible incorporated cloud storage space platforms.
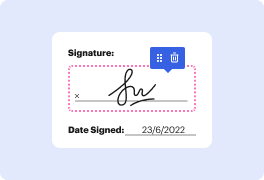
DocHub offers loss-free editing, eSignaturel collection, and ACL managing on a expert level. You don’t need to go through exhausting guides and spend hours and hours figuring out the application. Make top-tier secure document editing a typical process for the daily workflows.
hey whats up guys welcome to cert bros in this video were going to be talking about access control [Music] lists so what is an access control list access control lists also known as acls or simply access lists are rule-based lists that are used by switches and routers to identify traffic they can identify traffic based on the source address destination address and port numbers the most common use for an access list is to deny or permit traffic but there are other uses for access lists such as configuring network address translation and quality of service lets take a look at a quick example this router has an acl configured the acl is configured with rules that tell it which traffic is allowed to pass and which traffic is not for example we may want to allow all traffic destined for this server but at the same time we may want to block all other traffic to any other host this is all possible with a very simple access list okay so now we have an idea about what an access list does le