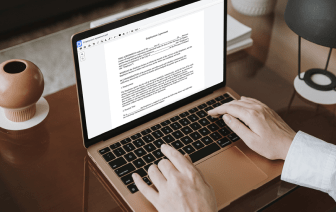
It is often difficult to get a platform that will deal with all of your organizational demands or offers you correct tools to handle document generation and approval. Picking an application or platform that combines crucial document generation tools that streamline any process you have in mind is critical. Although the most in-demand file format to use is PDF, you require a comprehensive software to handle any available file format, including DOCM.
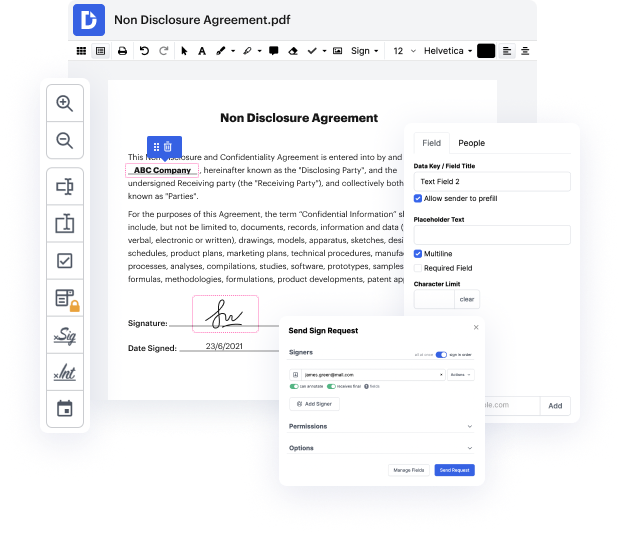
DocHub ensures that all of your document generation needs are covered. Revise, eSign, rotate and merge your pages based on your needs with a mouse click. Work with all formats, including DOCM, efficiently and . Regardless of the file format you start dealing with, you can easily convert it into a needed file format. Save a great deal of time requesting or looking for the appropriate document type.
With DocHub, you do not need more time to get used to our interface and editing process. DocHub is undoubtedly an easy-to-use and user-friendly platform for anybody, even all those without a tech education. Onboard your team and departments and enhance file management for the business forever. add PII in DOCM, generate fillable forms, eSign your documents, and have things carried out with DocHub.
Benefit from DocHub’s substantial feature list and swiftly work on any file in every file format, such as DOCM. Save time cobbling together third-party software and stick to an all-in-one platform to enhance your daily operations. Begin your free DocHub trial subscription today.
[Music] personally identifiable information what is pii pii is personally identifiable information that includes a persons name the names of family or friends addresses dates and places of birth social security numbers account numbers and even employee id numbers a personal data bdocHub occurs when pii is released to an unauthorized actor through email phishing attacks ransomware and even exploiting a victims digital footprints a digital footprint could be a potential piece of pii that exists on the internet as a result of a persons online activity easily harvested and then exploited by a threat actor cyber criminals can post ads on the dark web selling ones pii the identities are then bought by thieves to take part in tax fraud open fake accounts to apply for credit cards apply for work apply for a place to live and other exploitative crimes attackers can gather pii from anywhere including public forums and social media every type of organization businesses clinics and even school