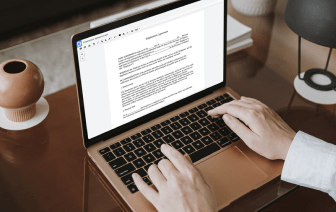
Unusual file formats in your day-to-day document management and editing operations can create instant confusion over how to edit them. You may need more than pre-installed computer software for efficient and fast file editing. If you want to add authentication in 602 or make any other basic alternation in your file, choose a document editor that has the features for you to deal with ease. To deal with all the formats, such as 602, opting for an editor that works properly with all kinds of files will be your best choice.
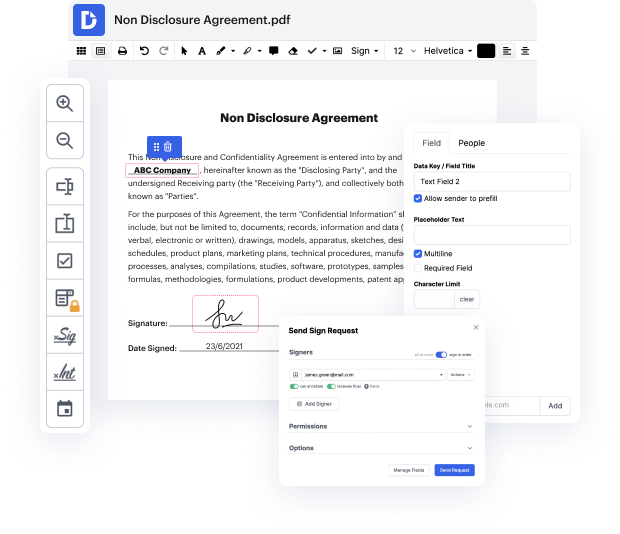
Try DocHub for efficient file management, irrespective of your document’s format. It has powerful online editing instruments that streamline your document management operations. It is easy to create, edit, annotate, and share any document, as all you need to access these features is an internet connection and an functioning DocHub account. A single document tool is all you need. Don’t lose time switching between different applications for different files.
Enjoy the efficiency of working with an instrument created specifically to streamline document processing. See how effortless it is to modify any file, even when it is the very first time you have dealt with its format. Sign up an account now and improve your entire working process.
In a previous video, we talked about the need for authenticating to a wireless network. And of course, there are many different ways that you could authenticate to a network, and weve used many of these different authentication methods on our different networks through the years. The most common type of authentication someone would use is their username and password. And its not unusual to add other types of authentication factors, along with the username and password. Although well sometimes use these authentication methods for wired networks, its very common to also see this on wireless networks. Thats mostly because wireless networks are sending and receiving into the air, and anyone who happens to be nearby with a wireless device could attempt to connect to that wireless network. Many of the types of authentication well use for wireless networks are built on a standard framework called the Extensible Authentication Protocol, or EAP. There are many, many different types of au